Overview
In March 2018, the Division of the Chief Information Officer rolled out a DNS filtering service to provide protection to network devices from known malicious Internet sites, including those harboring malware, viruses, phishes, and callbacks to botnet command and control centers.
Details
The intent of this new service, which supplements and expands similar services already implemented on the campus perimeter firewalls, is to reduce security incidents, decrease compromised systems on the network, reduce data loss, and improve the overall performance of the campus network.
The DNS filtering service checks DNS queries against a cloud-based, centralized, real-time security intelligence repository. If the site is classified as malicious, users will be redirected to a DNS page similar to the one shown below. However, if you believe the site you are trying to access is not malicious, you can use the "Report an incorrect block" link on that DNS page to report it as a false positive and submit a report for evaluation. Assessment will include contacting the provider for additional detailed information about why the site is blacklisted and if it proves reasonable the block will remain in place unless the user can provide additional justification for why access is needed for academic or business needs. This process may take up to 3 business days.
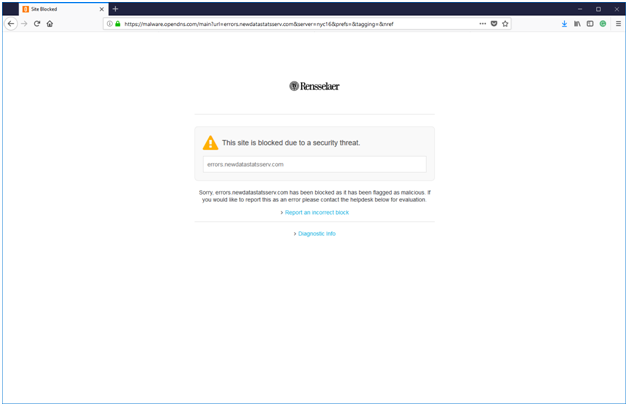
[Site Blocked dialog box stating that This site is blocked due to a security threat]
Comments
0 comments
Article is closed for comments.